How to deploy the Zeek Network Security Monitor on Ubuntu Server 22.04
[ad_1]
Zeek is a command-line network security monitoring tool that can be installed on a server in either your local data center or a third-party cloud host. Zeek monitors and records a number of different data points, such as connections, packets received and sent, and TCP session attributes. With this tool, you can trace events across your network to better ensure its security.
SEE: Password breach: Why pop culture and passwords don’t mix (free PDF) (TechRepublic)
Let’s get Zeek installed on an instance of Ubuntu Server 22.04, so your security teams can start checking up on the traffic bouncing in and out of your network.
Jump to:
What you’ll need to install Zeek
The only things you’ll need to install Zeek are a running instance of Ubuntu Server 22.04 or newer and a user with sudo privileges.
How to install Zeek
The first thing to be done is to log in to your Ubuntu Server instance. Once you’ve successfully logged in, install a trio of simple dependencies with the command:
sudo apt-get install curl wget gnupg2 -y
Next, change to the root user with:
sudo -s
Next, we must add the official Zeek GPG key with:
curl -fsSL https://download.opensuse.org/repositories/security:zeek/xUbuntu_22.04/Release.key | gpg --dearmor | tee /etc/apt/trusted.gpg.d/security_zeek.gpg
Add the Zeek repository with the command:
echo 'deb http://download.opensuse.org/repositories/security:/zeek/xUbuntu_22.04/ /' | tee /etc/apt/sources.list.d/security:zeek.list
Update apt:
apt-get update
Install Zeek with the command:
apt-get install zeek -y
During the installation, you’ll be asked how you would like to configure Postfix. Unless you already have a mail server up and running on the system, I would suggest configuring it as local only. You will have to log in to the server and check the admin users’ mail account to see any reports, which is done with the command mail.
If the mail command doesn’t exist, install it with:
apt-get install mailutils -y
Before we continue, make sure to add the Zeek installation path to your $PATH with:
echo "export PATH=$PATH:/opt/zeek/bin" >> ~/.bashrc
Source the bash file with:
source ~/.bashrc
How to configure Zeek
After the Zeek installation completes, you’ll need to make some changes to the configuration file. Open the file with:
nano /opt/zeek/etc/networks.cfg
You’ll want to add your network to the bottom of the default list, which will look something like this:
10.0.0.0/8 Private IP space172.16.0.0/12 Private IP space192.168.0.0/16 Private IP space192.168.1.0/16 Private IP space
Save and close the file. Next, open the main configuration file with:
nano /opt/zeek/etc/node.cfg
We will switch Zeek from the default standalone mode and into cluster mode. The first thing to do is comment out the following lines by placing a # at the beginning of each line:
[zeek]type=standalonehost=localhostinterface=eth0
Add the following to the bottom of the file, substituting SERVER with your hosting server’s IP address, and IFACE with the name of your networking interface:
[zeek-logger]type=loggerhost=SERVER
#[zeek-manager]type=managerhost=SERVER
#[zeek-proxy]type=proxyhost=SERVER
#[zeek-worker]type=workerhost=SERVERinterface=IFACE
#[zeek-worker-lo]type=workerhost=localhostinterface=lo
Save and close the file. Run a check on the configuration with the command:
zeekctl check
You should see output similar to this:
Hint: Run the zeekctl "deploy" command to get started.zeek-logger scripts are ok.zeek-manager scripts are ok.zeek-proxy scripts are ok.zeek-worker scripts are ok.zeek-worker-lo scripts are ok.
If everything checks out, deploy Zeek with:
zeekctl deploy
Once everything is deployed, check the status with:
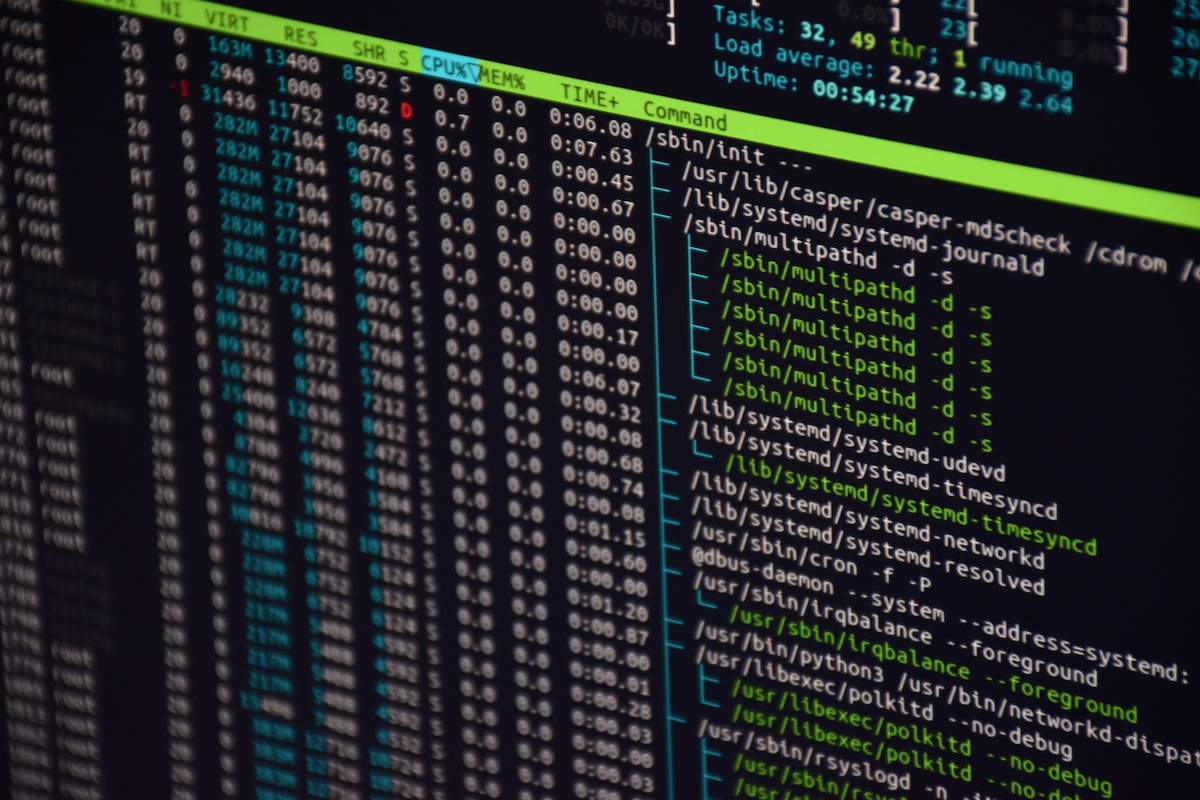
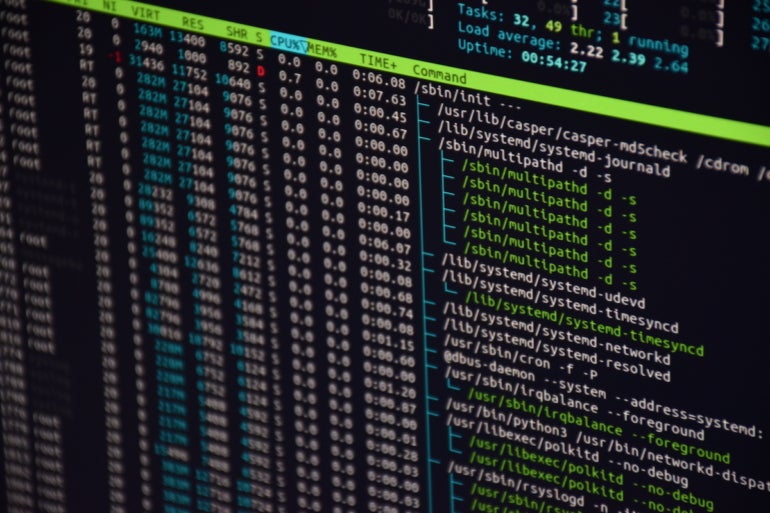
zeekctl status
You should see output similar to this:
Name Type Host Status Pid Startedzeek-logger logger 192.168.1.191 running 6366 06 Feb 13:18:44zeek-manager manager 192.168.1.191 running 6427 06 Feb 13:18:49zeek-proxy proxy 192.168.1.191 running 6488 06 Feb 13:18:54zeek-worker worker 192.168.1.191 running 6570 06 Feb 13:19:00zeek-worker-lo worker localhost running 6567 06 Feb 13:19:00
Zeek stores its logs in /opt/zeek/logs/current. You’ll find a log for broker, cluster, packet_filtering, conn, loaded_scripts, reporter, stats, stderr, stdout, telemetry and weird. The best way to view these logs is using the tail command to view them updated in real-time, like so:
tail -f /opt/zeek/logs/current/conn.log
That log file will display all real-time connections to the server.
Another handy trick you can try is viewing tcpdump information with Zeek. First, capture some packets with the command:
sudo tcpdump -i IFACE -s 0 -w mypackets.trace
Where IFACE is the name of the network device on the host. After giving that a few minutes to run, end the command with CTRL+C and then analyze the traffic with:
zeek -r mypackets.trace
Zeek will dump the log files into the current working directory. You should see the following log files: conn.log, dns.log, mypackets.trace, packet_filter.log, reporter.log and weird.log. Let’s say you then want to run one of Zeek’s built-in scripts against the captured packets. For that, you could issue something like this:
zeek -r mypackets.trace /opt/zeek/share/zeek/policy/frameworks/files/extract-all-files.zeek
You can check /opt/zeek/share/zeek for the different built-in scripts it offers.
Make Zeek yours
Zeek is a very powerful network monitoring tool. You’ll want to get up to speed with the various built-in scripts and even learn how to build your own. Until you reach that point, you can continue viewing the standard log files and capturing packages that enter and leave your server.
Subscribe to TechRepublic’s How To Make Tech Work on YouTube for all the latest tech advice for business pros from Jack Wallen.
[ad_2]
Source link The Zeek Network Security Monitor is an open-source platform for monitoring and securing networks. This powerful software tool offers features to help detect, analyze, and respond to security threats such as malware and intrusion attempts. As such, it is a crucial component of any organization’s infrastructure. Because of its extensive features, many organizations are utilizing Zeek in their security operations. However, if you’re interested in getting started with Zeek, there are several steps you need to consider when deploying it on a server running Ubuntu Server 22.04.
The first step is to install Zeek, which will require an Ubuntu repository. To do so, you must open the /etc/apt/sources.list file in an editor and add the following line:
deb https://download.opensuse.org/repositories/security:/zeek/xUbuntu_22.04/ /
Once this line is saved, you should run the following command to update the list of available repositories:
$ sudo apt-get update
Now, you can install Zeek using the command:
$ sudo apt-get install zeek
During the installation process, you may be prompted to allow automatic updates. It is recommended that you allow these updates in order to keep your system secure.
After completing the installation, you need to configure the Zeek daemon. To do so, open the /opt/zeek/etc/node.config file and configure the hostname, cluster, and so on. Make sure to save your changes after making the necessary alterations.
Finally, it’s time to start the Zeek daemon. To do so, open a terminal window and execute the command:
$ sudo service zeek start
This should start the Zeek service and you can check the status using the command:
$ sudo service zeek status
To ensure that the Zeek daemon is always running, it can be configured to automatically start when the server is rebooted. To do so, use the command
$sudo update-rc.d zeek defaults
Once the installation, configuration, and start up process is complete, Zeek should be up and running on your Ubuntu Server 22.04 instance. As such, you can now begin monitoring and securing your network with Zeek. With its vast array of features and capabilities, you can rest assured that your systems are always safe and secure.